Safe Authentication with Mobile Devices
Embrace a card-free authentication experience with YSoft MFX4 Mobile and Ultimate, with the fastest reading time for multi-format reading.

Seamless, Secure, and Versatile Authentication
 6-Year Product Warranty
6-Year Product Warranty
All readers come with enterprise-grade reliability, an industry-leading low failure rate of less than 0.5%, and a free six-year warranty.
 Latest Chip Technology
Latest Chip Technology
We've designed the MFX4 reader ranges using the latest chip technology to help you overcome supply chain woes.
 Supports +95% of Market Technology
Supports +95% of Market Technology
Our mobile readers (Mobile and Ultimate) support a wide range of technologies, including Legic, MiFare, Felica, and many more.
MFX4 Mobile
Reader for modern authentication
The MFX4 Mobile reader packs the top features of our readers into a portable design for card-free, convenient authentication.
- Connects to Apple Wallet
- Supports industry-leading credential solutions
- Pairs with the YSoft Mobile Connect app
Two-factor authentication
Access That’s Clever, Not Complicated
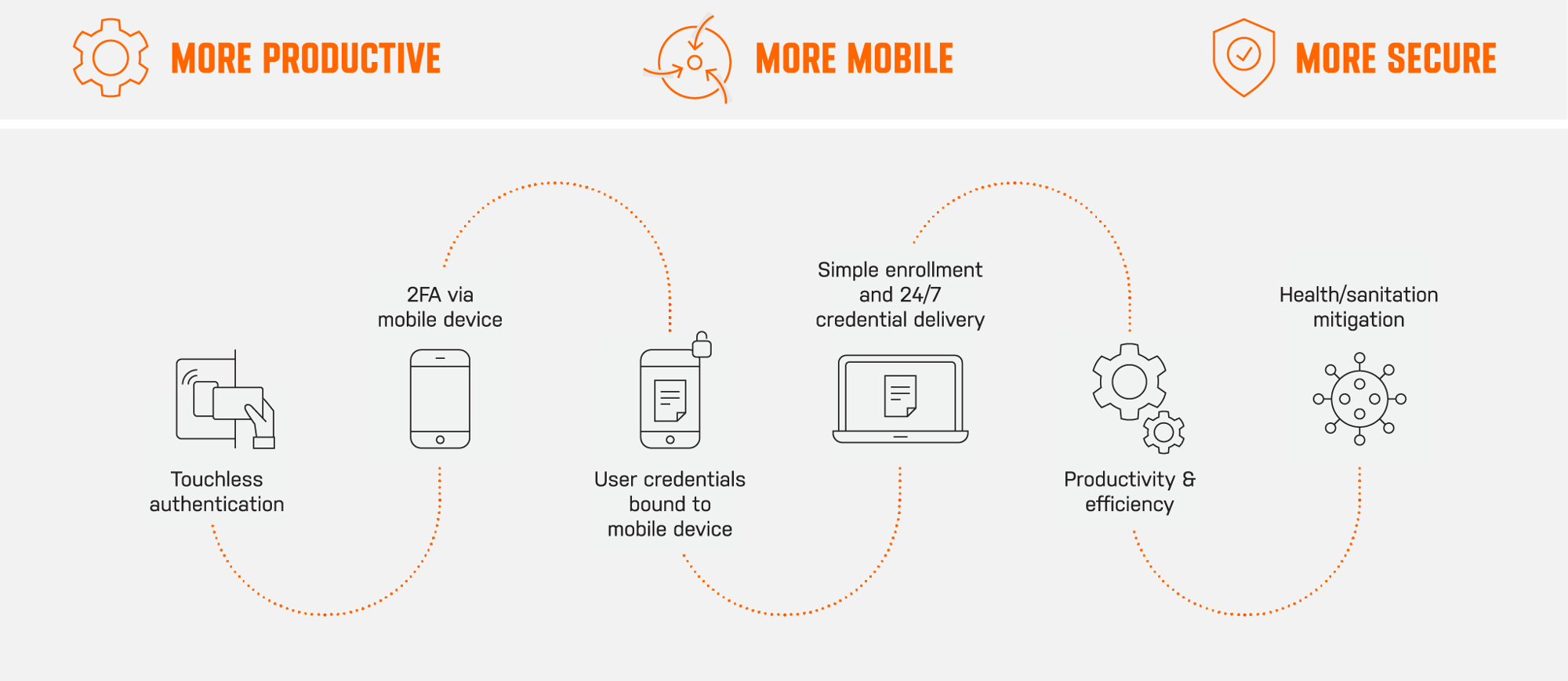
Secure logins by pairing encrypted app credentials with your phone’s PIN or biometric authentication to achieve two-factor authentication. Even if a phone is lost or stolen, it cannot be used to access your networked printers.

Contactless printing
Touch Nothing, Catch Nothing
Keep your office contamination-free and use MFX4 Mobile and Ultimate for mobile authentication on your printers. Authenticate on SAFEQ cloud and on-prem solutions with a simple wave of a phone, and let users print securely without touching the printer.
Explore SAFEQ Solutions
Reliable and Versatile Readers